Towards A Tokenized Data World: A New World Is Being Created | by Prof Bill Buchanan OBE | ASecuritySite: When Bob Met Alice | Medium

Debug Logging Microsoft.Identity.Client and the MSAL OAuth client credentials flow | Software Engineering
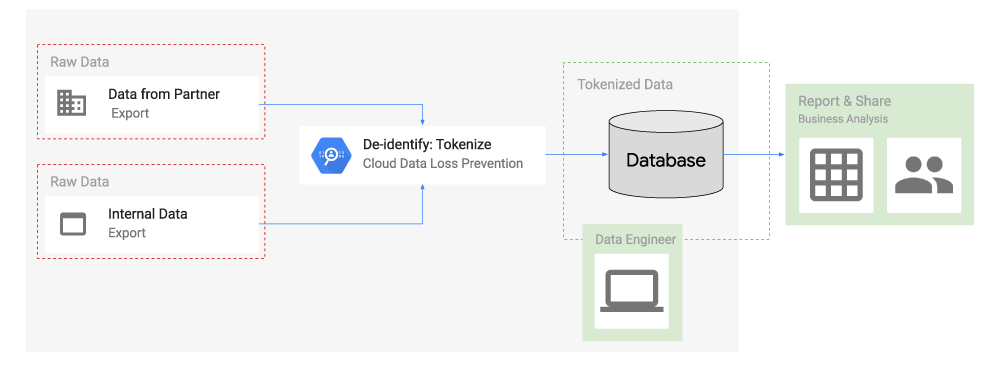
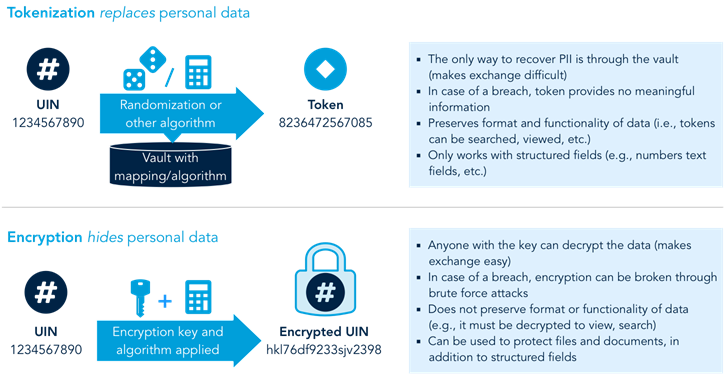
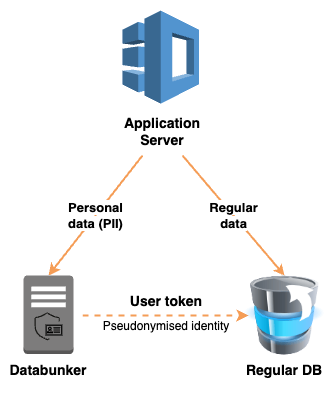
Take charge of your data: How tokenization makes data usable without sacrificing privacy | Google Cloud Blog











.jpeg)