Craig Rowland - Agentless Linux Security on Twitter: "The /proc/<PID>/stack area can sometimes reveal more details. We'll look at that like this: cat / proc/<PID>/stack In this case we see some network accept()

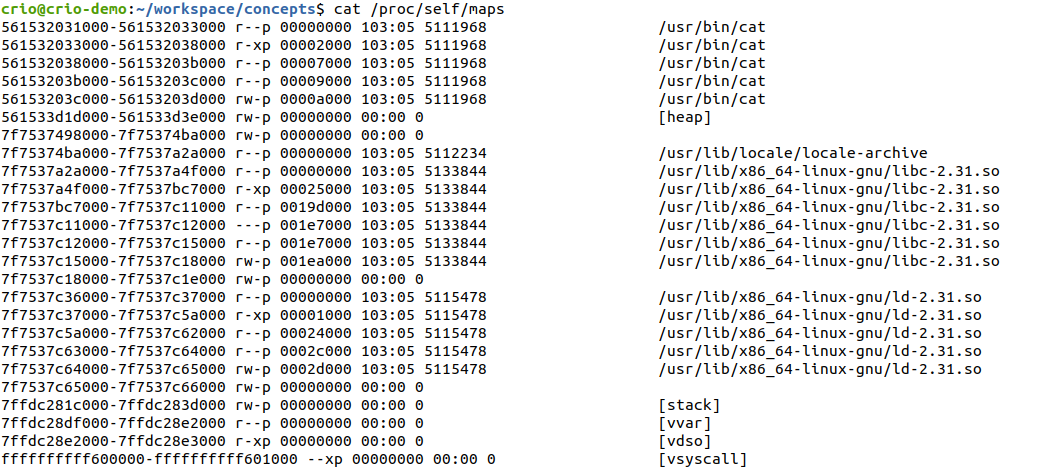
process - Why some libraries and other parts get repeated in the linux virtual memory with gdb? - Unix & Linux Stack Exchange
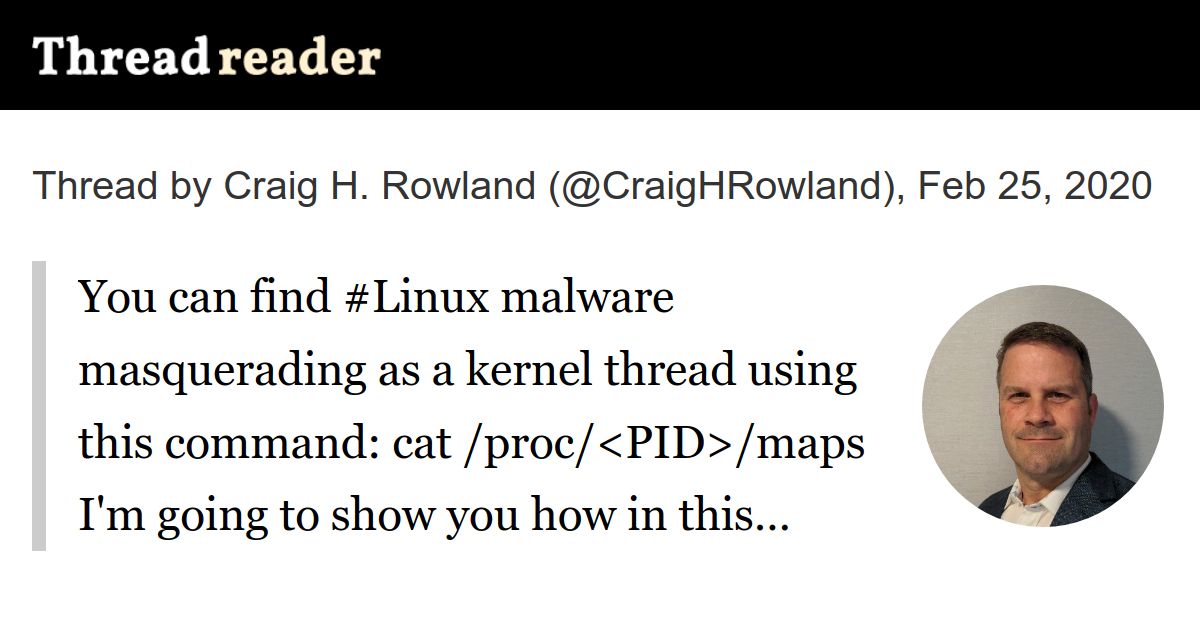
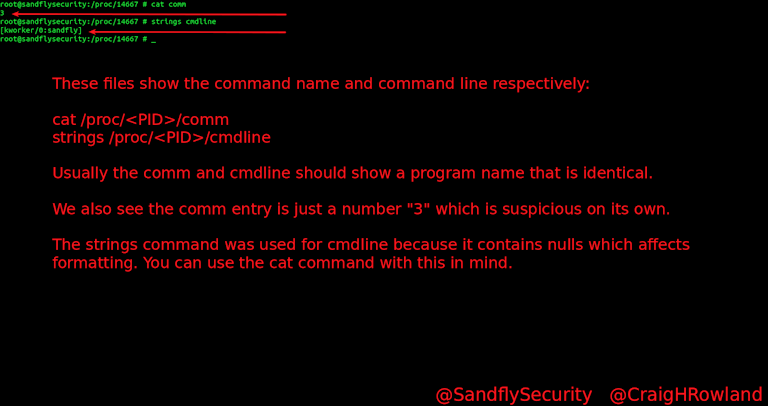
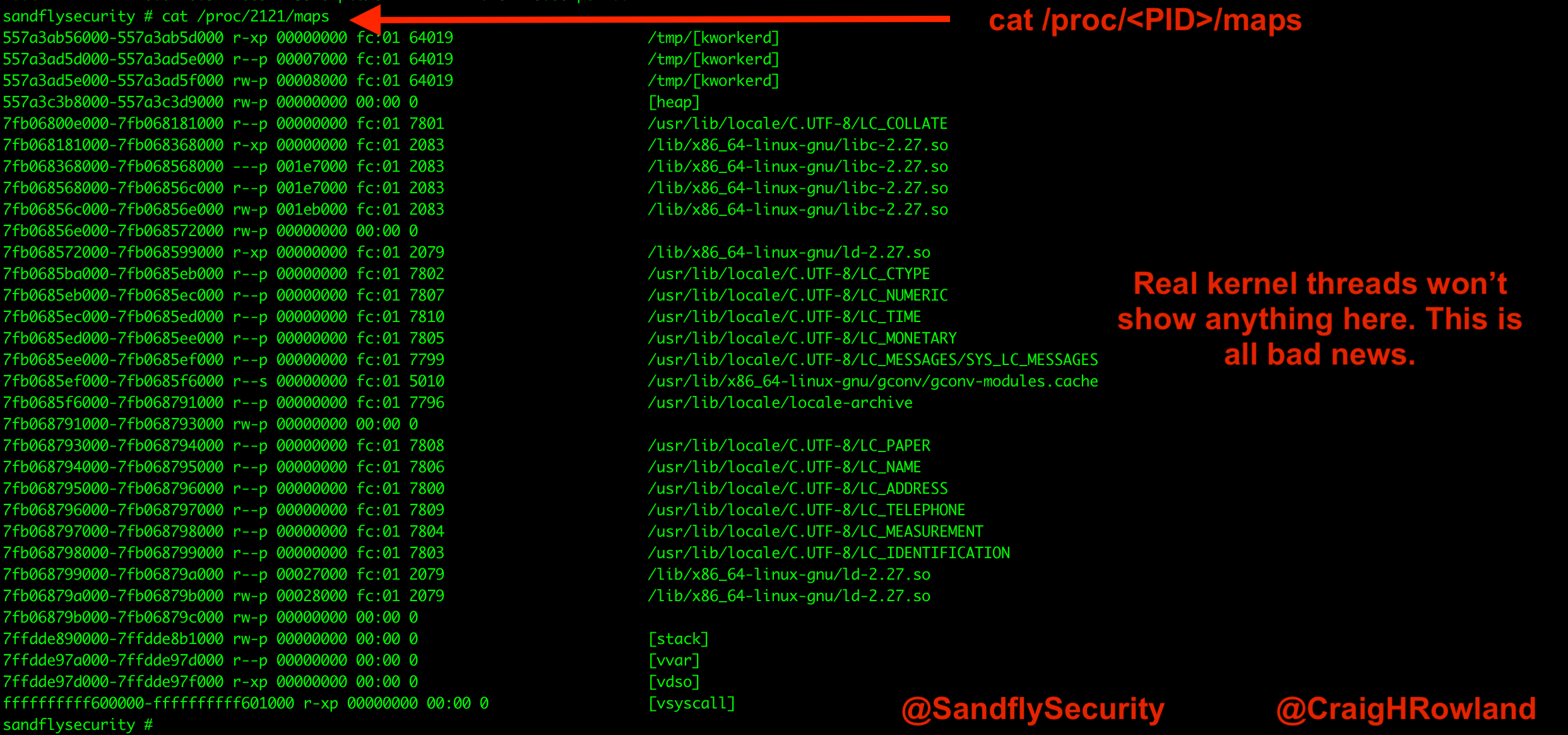
Thread by @CraigHRowland: You can find #Linux malware masquerading as a kernel thread using this command: cat /proc/<PID>/maps I'm going to show you how in this…







![Diving into /proc/[pid]/mem Diving into /proc/[pid]/mem](https://blog.cloudflare.com/content/images/2020/10/image3-25.png)