The Machine Age of Marketing: How Artificial Intelligence Changes the Way People Think, Act, and Decide | NIM - Nuremberg Institute for Market Decisions

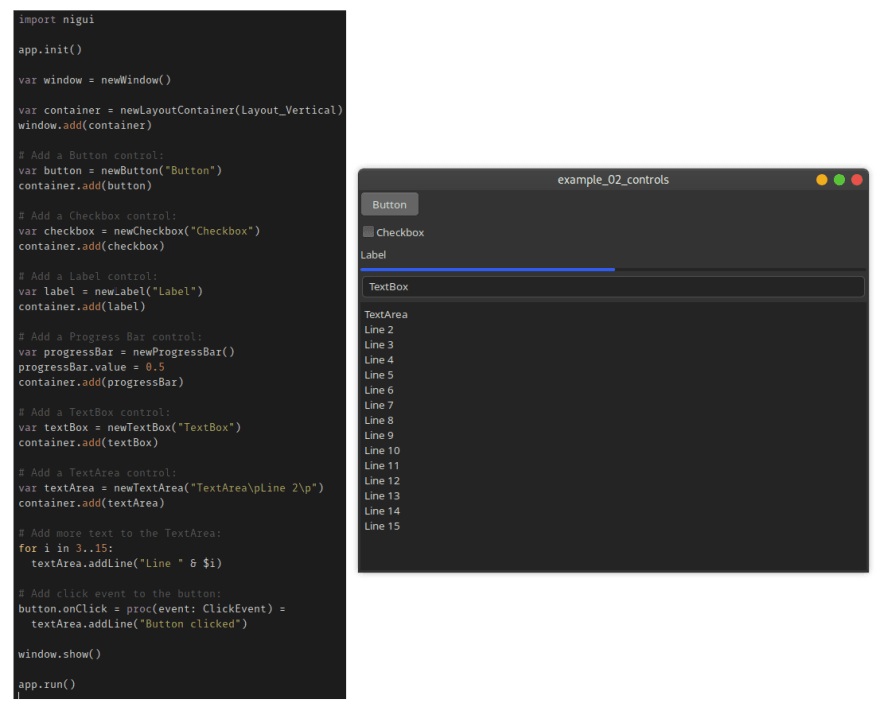
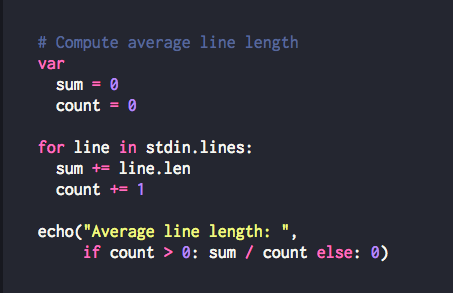
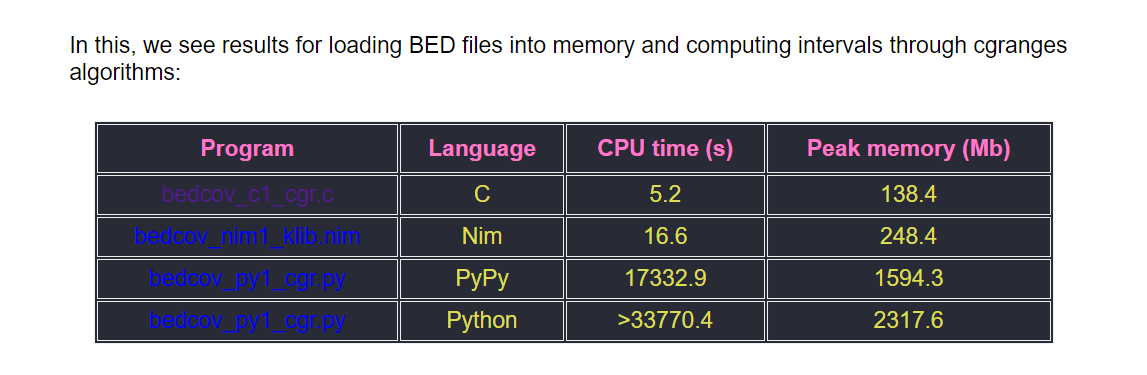
Could Nim Replace Python?. Why this fledgeling computer language… | by Emma Boudreau | Towards Data Science
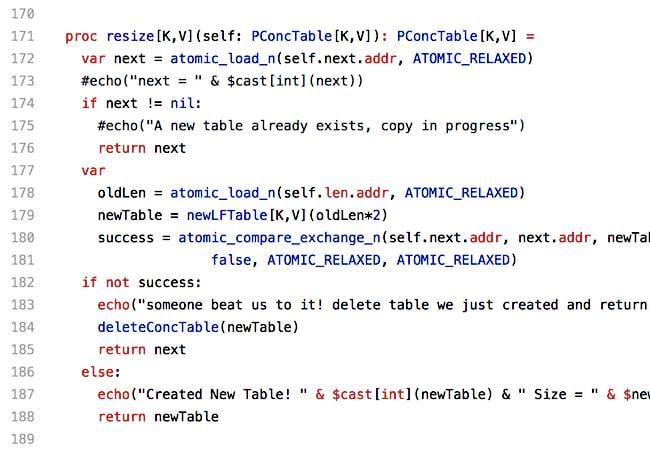
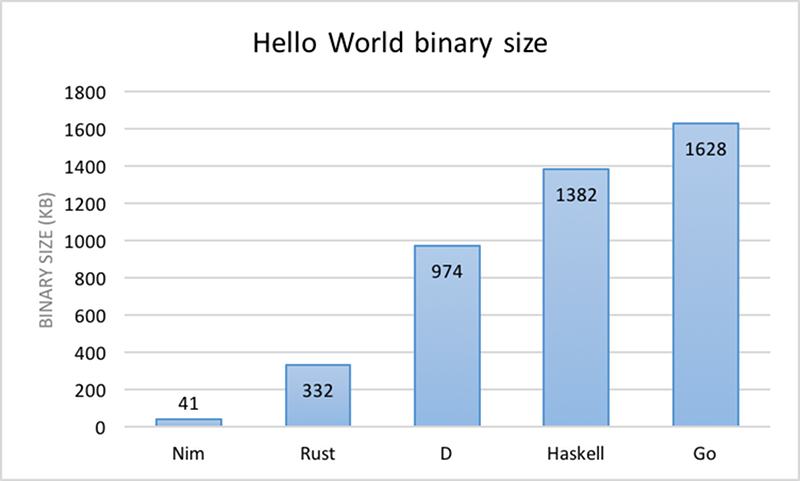
Are you a Nim-by? C-ish language, gentler than Go, friendlier than Rust, reaches version 1.0 • The Register

SD Times new digest: Databricks' MLflow 1.0, Nim programming language 0.20, and Visual Studio Code 1.35 - SD Times
An Intro to NIM: The Python-Like Programming Language Used By Malicious Ransomware Developers | HackerNoon

Mastering Nim: A complete guide to the programming language: 9798836539412: Computer Science Books @ Amazon.com

AI and the Machine Age of Marketing Vol. 11 No. 2 (2019) by NIM - Marketing Intelligence Review - Issuu

Could Nim Replace Python?. Why this fledgeling computer language… | by Emma Boudreau | Towards Data Science

Mastering Nim: A complete guide to the programming language: 9798836539412: Computer Science Books @ Amazon.com